3D Risks
3D Printing Offers New Risk Challenges
As commercial 3D printing advances from occasional to routine use, the product liability landscape will shift around it. Defective and counterfeit product exposures, among others, will arise for all participants along the manufacturing continuum, industry experts said.
In an adverse incident, said Rob Gaus, product risk leader, Marsh, liability will be apportioned among participants in the manufacturing and distribution stream: product manufacturer, printer manufacturer, software designer, feedstock supplier, distributor (especially if it modifies the product) and retailer (if the manufacturer is not well capitalized). No case law exists yet.
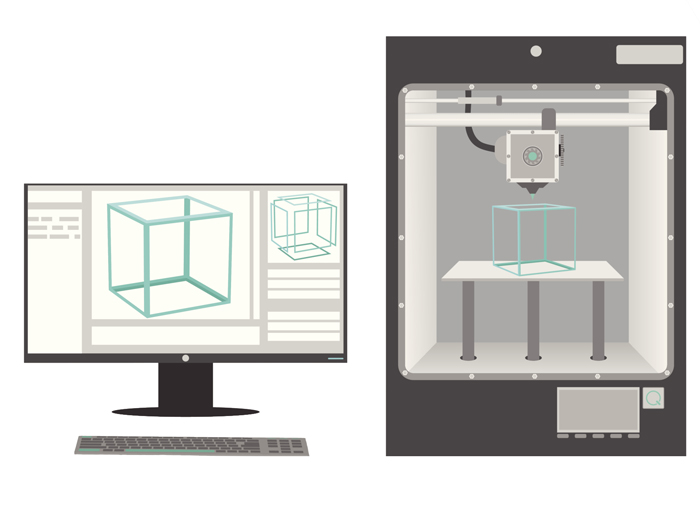
In 3D printing, a computer sends the software containing a product design to one or more printers, which builds the product, layer by layer, from many kinds of materials — plastics, metals, drugs, paints and even human tissue.
David Carlson, U.S. manufacturing and automotive practice leader, Marsh, said 3D-printed products are treated the same as any other new operation that poses new risks.
Underwriters and brokers must first assess the company’s risk management profile and risk appetite. When production, research and development teams look at technology, “they should loop in risk management. Risk management should be part of the continuum, or the company could get into sticky situations.”
The emerging risks include unregulated manufacturing, said Mark Schonfeld, a partner at Burns & Levinson LLP in Boston specializing in business and intellectual property law.
If 3D printing enables production of, say, just 100 hip implants or 100 hearing aids, such work will generally take place outside of a traditional mass-production factory, which is subject to government regulation and inspection.
“Insurance companies like FDA oversight of manufacturing because it makes products safer and helps identify responsibility when things go wrong,” Schonfeld said.
To protect themselves and their clients, Schonfeld advises insurers to keep abreast of technological developments, consult with a creative and knowledgeable attorney about how to address liability exposure, and adjust existing policies to be fair to consumers and prevent injury to the insurance company.
3D printing also raises the risk of counterfeit products, said Peter Dion, line of business director-product liability, Zurich Insurance. The digital “recipe” in the software design, and is vulnerable to capture, he said.
Although there is no encryption mechanism for the software, one solution might be to transfer the digital file in pieces only as they are needed by the printer to prevent capture of the entire design signature, Dion said.
Manufacturers have always struggled with counterfeit products, but 3D printing magnifies the risks because it can slash the time from product development to market-ready product to a matter of hours and requires no molds or prototypes. “Hackers can take the proprietary blueprint or software, send it to a third-world country, and have the product ready for market tomorrow,” said Carlson. “That’s a business disruption issue. Counterfeiters can put a company out of business.”
Drug manufacturers may subvert counterfeiters by adding tracer elements and watermarks to their formulations, which protects their reputations, profits and public health. “If the counterfeiters get the recipe wrong, they might not produce high-quality drugs for public consumption,” Carlson said.
Other manufacturers can also use watermarks and digital rights management (DRM) software to prevent file sharing. Still, Carlson said, counterfeiting is an old problem. “Bad guys have always exploited new technologies for their personal gain.”
The materials used by manufacturers present a greater potential loss exposure than the 3D printer itself, said Dion, noting that it is just another piece of equipment, like a pencil or a lathe.
For example, if a 3D printer is used to replicate a cupcake, the manufacturer should be as careful of contaminants in the mix as traditional bakers need to be. “When 3D printer manufacturers purchase materials from suppliers, they need to perform due diligence on their supplier’s products also.”










